How Single Sign on Authentication Work?
Introduction:
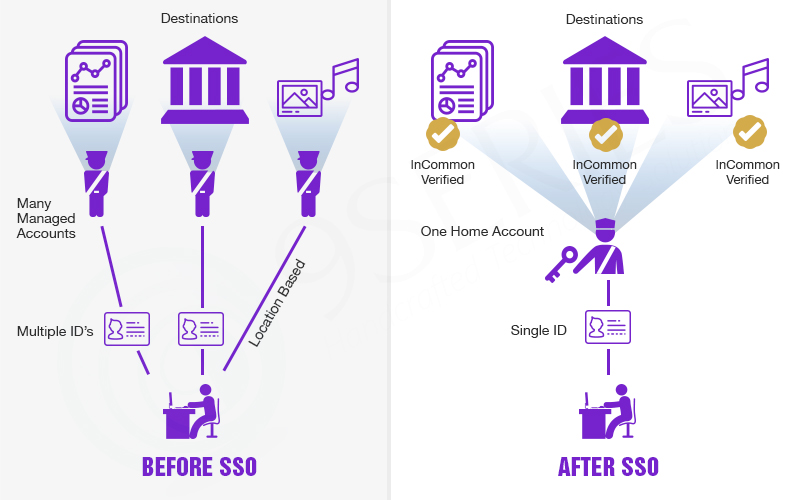
Single sign on is a session and user authentications service that allows a one-click access to all your applications with one password on common DNS parent domain.
For eg. Authenticating in your Gmail account doesn’t require to do the same in youtube, google drive, and other google services.
It usually makes use of “Central Services” which orchestrates the single sign-on between multiple devices. For eg., Google uses Google Accounts. When user first login, Google Account creates the cookie and it persists with the user as they navigate other Google-owned services.
As various applications and resources bolster different authentication mechanisms, single sign-on have to translate internally and store different credentials associated with what is used for initial authentication.
Why we need SSO?
Consider the scenario where user authenticates to domain X and he/she wants to authenticate in domain Y with same credentials. It may not be possible for the user because both credentials store in different cookies.
How does it work?
The concept of the single sign-on using Asp.net mechanism is simple. There is something we create called Central Domain. The authentication is performed through “central domain” and after that, the session is shared to other domain in the same way.
The central domain generates JSON web token and it is passed to the client and other authentication domain.
Why we go for Single Sign On?
Authentication is a horizontal requirement across multiple platforms, applications, and infrastructures. There is no need for the user to have multiple usernames. Ideally, he/she has to identify and provide access to all authorized network resources.
The main objective of SSO is to allow user access to all applications from a single login. It provides a unified mechanism to manage and authenticate users and implement business rules which determine user access to all authorized network resources.
There are some benefits of SSO which is listed below:
Improved user productivity:
The user does not have to log in by multiple logins and no more multiple usernames and passwords. SSO supports the personal answer’s fewer request to recover/reset forgot password.
Improved developer productivity:
SSO provides the developer with a common authentication framework. If SSO mechanism is different, then they don’t have to worry about the framework.
Simplified administration:
The burden of managing user account is simplified when the application participates SSO protocol. The level of simplification depends upon the applications because SSO simply deals with authentication.
Problems with SSO mechanism:
Difficult to retrofit:
SSO can be difficult , time-consuming and expensive to implement on the application.
Unattended desktop:
There are some security risks with SSO. If the user walks away from machine with logged in, then malicious user could gain user’s resources. With SSO, all authorised resources are compromised.
Single point attack:
SSO uses central authentication service. It is attractive target of hackers who may decide to carry out a denial service attack.
SSO Frameworks:
1. Open SSO
2. JOSSO(Java Open Single Sign On)
3. SAML(SSO service for google apps)
Other Services:
There are many other authentication schemes like OAuth, OpenID, OpenID Connect and Facebook Connect. But the main difference is that in other services, it provides the way of accessing other websites by their own behalf.
We, 9series has a dedicated team of Asp.net developers and they had successfully implemented SSO mechanism in an organization and also to client for web applications to make an end user authentication simple and secure.
Recent Posts
Deep Learning Explained: Understanding the Brain Behind AI
The Intersection of AI and IoT: Creating Smarter, Connected Environments
The Evolution of AI: From Simple Algorithms to Neural Networks
The Role of AI in Sustainable Development
Scaling New Heights: Integrating Advanced Technologies in Startup Product Engineering